HBSCYBERSECURITY
Managed XDR
Intercept attacks at the earliest stages and constantly adapt to an ever-changing threat landscape.
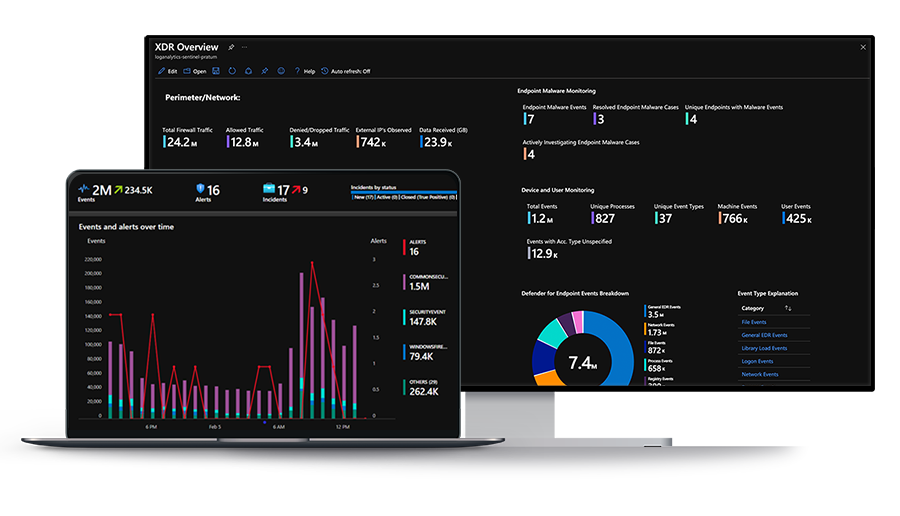
Extended detection and response. 24x7 security operations.
HBS Managed XDR includes:
- 24x7 Security Operations Center service and support
- Security information and event management
- Endpoint detection and response
Ready for around-the-clock protection?
We can help.
Our U.S.-based SOC onboards each client with a collection of custom workbooks then continues to tune the system for your unique environment.
Customized Experience
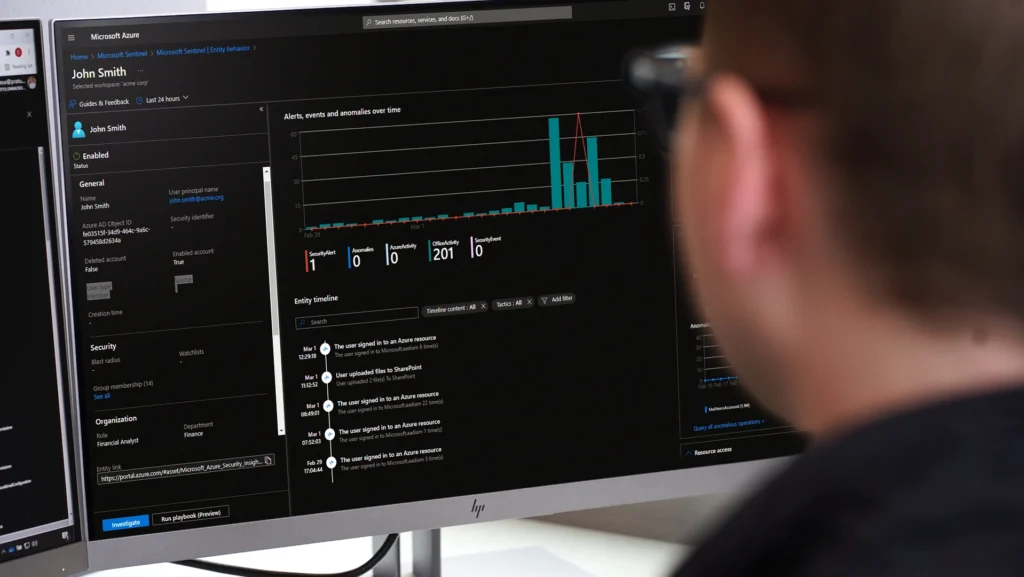
HBS analysts design unique security playbooks based on each client's business and technology environment. These unique rulesets enable our analysts to properly identify and respond to security threats. Custom workbooks let you review how Managed XDR is protecting your environment at any time—and prove the service’s ROI. Talk to Sales
Essential Security Knowledge
When something suspicious happens, our SOC analysts review the alerts and let clients know when they need to act. We deal with false positives so you don’t have to. Our team continually revises security playbooks to efficiently deliver meaningful alerts and automated responses. We deploy user behavior and analytics (UEBA) detection to end alert fatigue and detect sophisticated rogue activity that poses a legitimate threat to the confidentiality, integrity, and availability of client information. Talk to Sales

24x7 Confidence
Why Managed XDR by HBS?
We Use the Right Technology
A cloud-native SIEM (Microsoft Sentinel) and enterprise endpoint detection and response platform (Microsoft Defender for Endpoint) backed by decades of security experience and monitoring of billions of daily events.We Have a Dedicated Team
Our SOC analysts work with you to understand your environment and tune the Managed XDR service to fit your needs.We Deliver a Meaningful Return
We eliminate alert fatigue by reducing millions of monthly events to a handful of alerts that require your attention.Interested in Managed XDR?
Request a meeting with one of our experts today.






